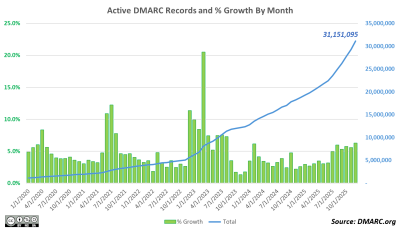
It has been several years since the statistics for DMARC policy records had been updated on this page. The main reason for this was surges of up to millions of records each quarter, if not each month. They would show up, demanding analysis and explanation, and then in many cases most of them would diappear […]